Author : ESG
“`html
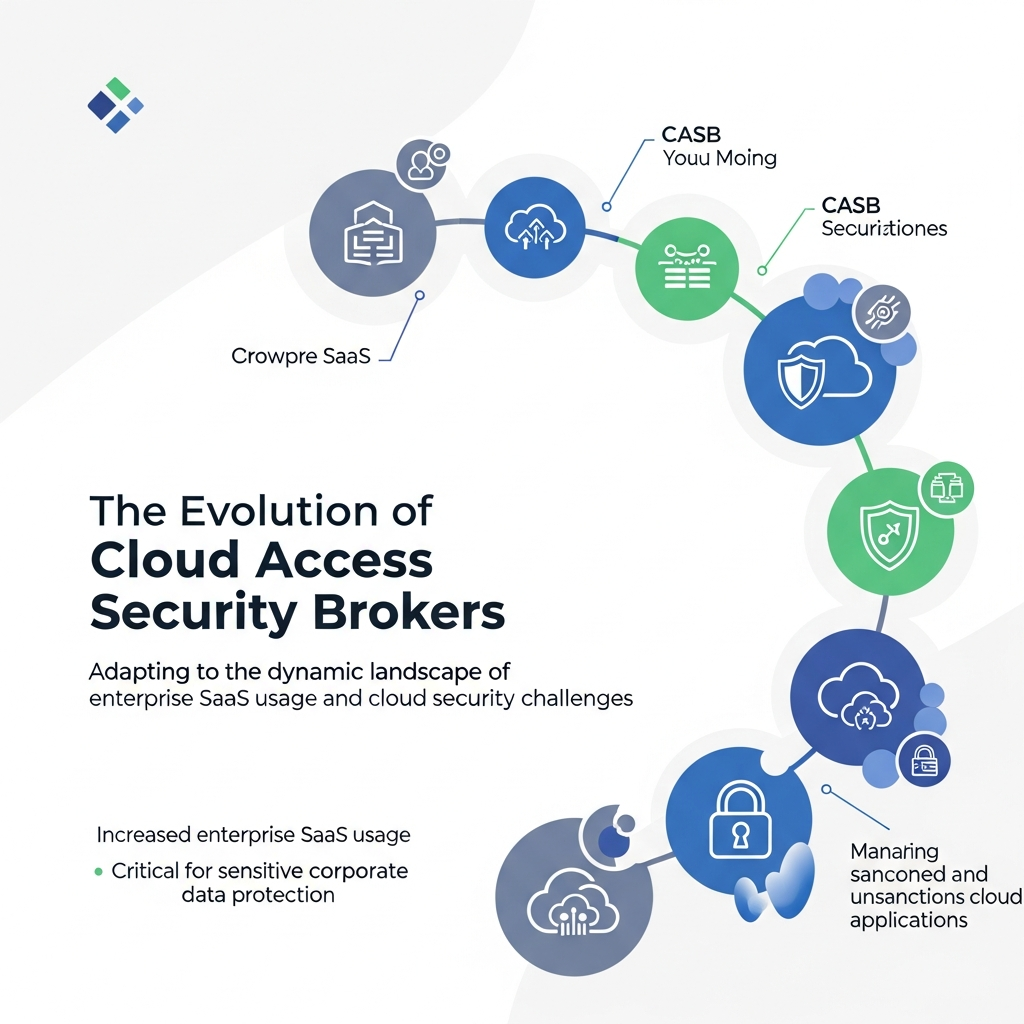
The Evolution of Cloud Access Security Brokers
Summary
Cloud Access Security Brokers (CASBs) have become indispensable in today’s cloud-centric world. This blog post explores the evolution of CASBs, from their initial emergence to their current sophisticated capabilities. You’ll learn how CASBs protect your organization’s sensitive data, adapt to the changing threat landscape, and integrate with modern security strategies. We’ll also cover best practices and answer frequently asked questions to help you understand and leverage CASBs effectively.
Introduction
Welcome to a journey through the evolution of Cloud Access Security Brokers (CASBs). In an era where cloud adoption is no longer a trend but a fundamental aspect of modern business, understanding CASBs is crucial. From managing core business applications to housing sensitive data, the cloud has become the backbone of many organizations. This shift, combined with the proliferation of unsanctioned cloud applications (shadow IT), has amplified the need for robust security solutions. That’s where CASBs come in.
When CASBs first appeared, the enterprise SaaS landscape was significantly different. The initial focus was often on basic visibility and control. Today, however, CASBs have evolved into comprehensive security platforms that address a wide range of threats and challenges. Let’s dive deeper into their fascinating evolution.
Early Days: Addressing the Shadow IT Challenge
The early 2010s saw the rise of cloud applications, often adopted by employees without the IT department’s knowledge. This “shadow IT” created significant security and compliance risks. Initial CASBs focused on:
- Visibility: Discovering which cloud applications were in use.
- Access Control: Managing user access to sanctioned and unsanctioned apps.
- Data Loss Prevention (DLP): Basic DLP capabilities to prevent data leakage.
These early solutions provided a critical first step in securing cloud environments. However, they lacked the sophistication needed to address the increasingly complex threat landscape.
The Rise of Advanced Threat Protection
As threats evolved, so did CASBs. Today’s CASBs offer advanced threat protection, including:
- Threat Detection: Using machine learning to identify and respond to unusual user behavior.
- Malware Protection: Scanning files for malware before they are uploaded to the cloud.
- Insider Threat Detection: Monitoring for malicious activities from within the organization.
- Integration with SIEM and SOAR: To streamline security workflows and automate responses.
Data Loss Prevention and Compliance
Data protection and compliance have always been central to CASB functionality, with a significant upgrade in recent times.
- Advanced DLP: Improved data classification and contextual analysis.
- Compliance Enforcement: Supporting compliance with regulations such as GDPR, HIPAA, and PCI DSS.
- Data Encryption: Encryption capabilities for sensitive data stored in the cloud.
Key Factors Driving CASB Evolution
Several key factors have driven the evolution of CASBs:
- Increased Cloud Adoption: As more organizations migrate to the cloud, the need for robust security grows.
- Sophisticated Threats: Cyber threats have become more complex, requiring advanced security solutions.
- Regulatory Requirements: Compliance with data protection regulations has become stricter.
- Hybrid IT Environments: The rise of hybrid IT environments necessitates CASBs that can protect data across on-premises and cloud environments.
Tips for Choosing and Implementing a CASB
To maximize the effectiveness of a CASB, consider the following tips:
- Assess Your Needs: Understand your organization’s specific security requirements and cloud usage.
- Evaluate Vendors: Research and compare different CASB vendors based on their features, capabilities, and pricing.
- Prioritize Integration: Ensure the CASB integrates seamlessly with your existing security infrastructure.
- Plan for Deployment: Implement the CASB in phases, starting with visibility and control, then gradually adding advanced features.
- Provide Training: Educate your employees on cloud security best practices and the role of the CASB.
Conclusion
The journey of Cloud Access Security Brokers reflects the dynamic nature of cybersecurity. From addressing shadow IT to providing advanced threat protection and compliance enforcement, CASBs have become essential tools for securing the modern cloud environment. As you navigate the ever-evolving landscape of cloud security, remember to stay informed, adapt to emerging threats, and leverage the power of CASBs to protect your valuable data. Embrace the future with confidence, knowing that your security infrastructure is equipped to handle whatever comes next.
Frequently Asked Questions (FAQ)
A CASB is a security policy enforcement point that is placed between cloud service users and cloud service providers. It combines and integrates multiple security enforcement capabilities.
CASBs provide visibility, compliance, data security, and threat protection for cloud services.
CASBs can operate in different modes, including reverse proxy, forward proxy, API-based, and inline modes, each offering different levels of control and protection.
CASBs help organizations gain control over cloud app usage, enforce security policies, protect sensitive data, and ensure compliance with regulatory standards.
Consider your specific security needs, cloud usage, integration requirements, and budget when selecting a CASB vendor.
“`